
- SAP Community
- Products and Technology
- Technology
- Technology Blogs by SAP
- SSO Configuration on Asset Management steps involv...
Technology Blogs by SAP
Learn how to extend and personalize SAP applications. Follow the SAP technology blog for insights into SAP BTP, ABAP, SAP Analytics Cloud, SAP HANA, and more.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Advisor
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
05-17-2023
11:11 PM
SSO based on Principal Propagation for SAP Asset Manager
Agenda:
Single Sign-on Authentication Types:
Single Sign-on based on Principal Propagation for SAP Asset Manager (BTP)
Principal Propagation -process Flow
Principal Propagation: Architecture Overview
technical landscape
Principle Propagation Compatibility
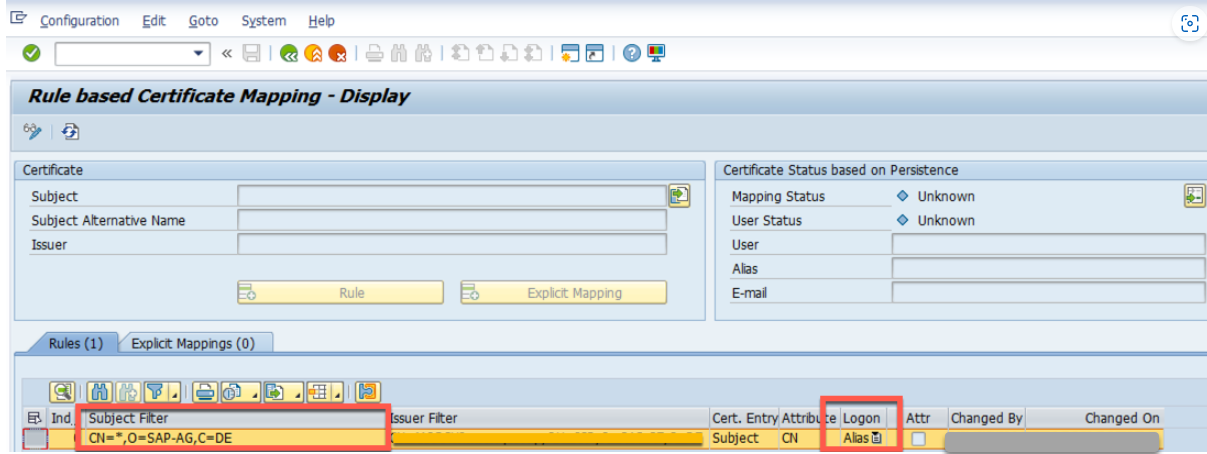
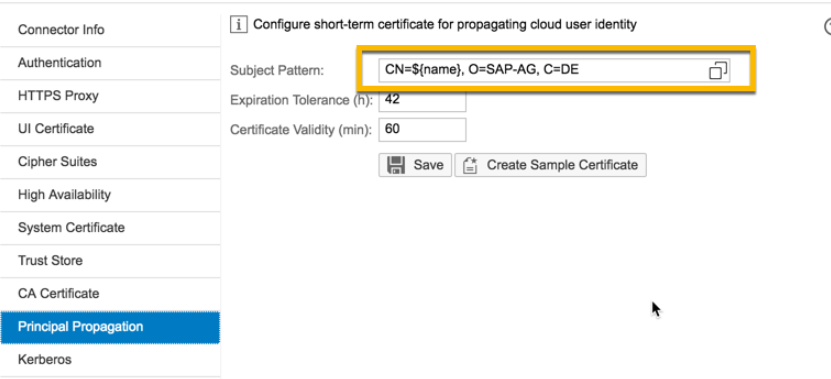
In the context of the SAP Mobile Add-On, the authorization expectation is for the SAP Cloud Connector to pass the cloud user identity through principal propagation in a subject pattern that is matched to a matched alias in the back end system.
SAP uses Rule based certificate mapping
Set the Principal propagation.
Step1.
SAP Cloud platform authentication setup using IAS with Azure AD
Connection to Corporate Active Directory need to establish.
Prerequisite: Cloud connector is installed and connected to SCP subaccount
Step 2.
Check the BTP
click on Local Service Provider and edit & click on Get Metadata and upload in the IAS.
Step 3.
Go to IAS tenant.
Application & Add new Application.
Give the name to the Application.
Application Display Name:
Application Home URL: keep empty.
Application Type:
Step 4.
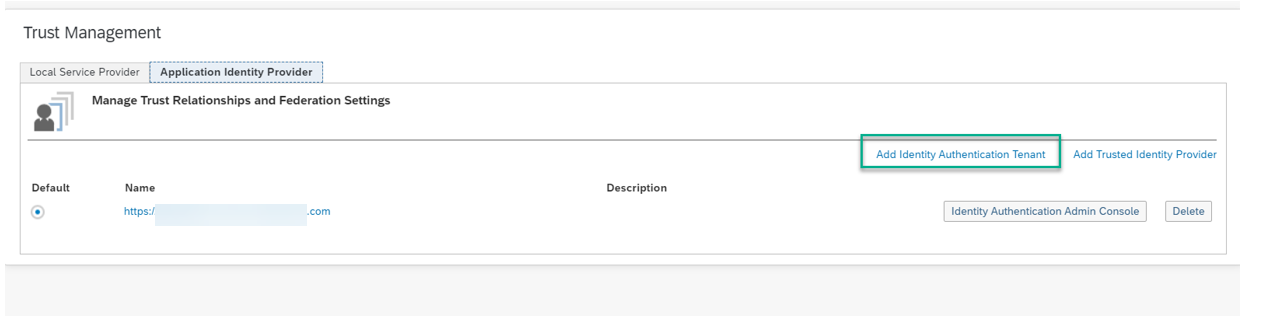
Go to SAP BTP Cockpit
On Trust, create a Trust Management
Add identity Authentication Tenant (we have two tenant one is used for development & quality and other is used for production.
Select the trail and confirmation popup will appear.
download the metadata.
Step 5.
Go to IAS --> Application --> Bundled Applications --> where you have created the Asset manager DEV.
Define from Metadata (upload the metadata which you have downloaded.
check the SAML 2.0 Configuration and signing Certificates.
check SHA-256 and Sign assertions is oN and sign single logout message is on and require signed single logout messages.
Save
Step 6.
Steps for IAS -Azure AD
SAML 2.0 Configuration -->go to Tenant settings and under the Assertion consumer service end point you see the metadata where you can download the metadata.
Step 7:
Upload the metadata into Azure AD
To configure the integration of SAP cloud platform Identity Authentication into Azure AD, you need to add SAP Cloud Platform Identity Authentication from the gallery to your list of managed SaaS apps.
Sign into the Azure portal using either a work or school account to Microsoft account.
in the left navigation pane, select the Azure Active Directory service.
navigate to Enterprise Applications and then select App applications.
to Add new application, select New Application
in the Add from the gallery section, type SAP Cloud Platform Identity Authentication in the search box. select SAP cloud Platform Identity Authentication from results panel and then add the app.
wait a few second s while the ap is added to your tenant.
download the metadata.
Login to IAS and upload the metadata in IAS.
Go to Identity Authentication Service --> Corporate Identity Providers --> create --> Add identity Provider & define the Metadata.
select the Microsoft ADFS/Azure AD as the Identity Provider Type
Enable the Single Sign on button & go to conditional Authentication and select the Default identity provider.
Enable Single Sign-on
Set conditional Authentication.
Save
Go to BTP
Security à Trust à Add - Identity Authentication Tenant / Trusted Identity Provider
& Add-Trusted identity Provider & upload the IAS metadata which you have downloaded
Click on the Add-Trusted identity Provider & upload the IAS metadata which you have downloaded.
Create a group in IAS tenant for “Administrators” of Cloud Platform mobile services
Login to IAS
Go to Applications and Budled Applications (Assertion Attribuites)
Cloud Platform Account Configuration
Now, the Cloud Platform account needs to be configured to map the IAS_CPms_Admin group to a group that is granted the desired roles.
Navigate to the “Authorization Management” screen in Cloud Platform cockpit. Go to the “Groups” tab and click on “New Group”. Create a new group called “MobileServiceAdmin
Similarly create Group “MobileServiceUser” and assign the roles mentioned. This is required for Mobile app users.
SCP/BTP - Navigate to Trust Management screen, click on “Application Identity Provider” tab and click on the trusted IdP setting that represents the IAS tenant account
Login to BTP
Similarly add the Group for Mobile App user
Now, navigate to “Configure development & Operations Cockpit” (refer to the screen in step 5) and click on “Roles”. Create a new role “MobileServicesCockpitAdministrator” and assign it to the group “MobileServiceAdmin”.
Click on “Destinations & Permissions”. Edit the application permissions and select the role “MobileServicesCockpitAdministrator” and save.
Flow chart for Troubleshooting the issue.
Agenda:
Single Sign-on Authentication Types:
Single Sign-on based on Principal Propagation for SAP Asset Manager (BTP)
Principal Propagation -process Flow

Principal Propagation: Architecture Overview

technical landscape

Principle Propagation Compatibility
In the context of the SAP Mobile Add-On, the authorization expectation is for the SAP Cloud Connector to pass the cloud user identity through principal propagation in a subject pattern that is matched to a matched alias in the back end system.
SAP uses Rule based certificate mapping
Backend user names

Set the Principal propagation.
Step1.
SAP Cloud platform authentication setup using IAS with Azure AD
Connection to Corporate Active Directory need to establish.
Prerequisite: Cloud connector is installed and connected to SCP subaccount

Cloud Connector configuration
Step 2.
Check the BTP

BTP Cockpit
click on Local Service Provider and edit & click on Get Metadata and upload in the IAS.
Step 3.
Go to IAS tenant.

IAS Home screen
Application & Add new Application.

Add Application
Give the name to the Application.
Application Display Name:
Application Home URL: keep empty.
Application Type:
Step 4.
Go to SAP BTP Cockpit
On Trust, create a Trust Management

Add identity Authentication Tenant (we have two tenant one is used for development & quality and other is used for production.
Select the trail and confirmation popup will appear.

download the metadata.
Step 5.
Go to IAS --> Application --> Bundled Applications --> where you have created the Asset manager DEV.

Define from Metadata (upload the metadata which you have downloaded.
check the SAML 2.0 Configuration and signing Certificates.
check SHA-256 and Sign assertions is oN and sign single logout message is on and require signed single logout messages.
Save

Step 6.
Steps for IAS -Azure AD
SAML 2.0 Configuration -->go to Tenant settings and under the Assertion consumer service end point you see the metadata where you can download the metadata.

Step 7:
Upload the metadata into Azure AD
To configure the integration of SAP cloud platform Identity Authentication into Azure AD, you need to add SAP Cloud Platform Identity Authentication from the gallery to your list of managed SaaS apps.
Sign into the Azure portal using either a work or school account to Microsoft account.
in the left navigation pane, select the Azure Active Directory service.
navigate to Enterprise Applications and then select App applications.
to Add new application, select New Application
in the Add from the gallery section, type SAP Cloud Platform Identity Authentication in the search box. select SAP cloud Platform Identity Authentication from results panel and then add the app.
wait a few second s while the ap is added to your tenant.
download the metadata.



Login to IAS and upload the metadata in IAS.
Go to Identity Authentication Service --> Corporate Identity Providers --> create --> Add identity Provider & define the Metadata.

select the Microsoft ADFS/Azure AD as the Identity Provider Type

Enable the Single Sign on button & go to conditional Authentication and select the Default identity provider.

Enable Single Sign-on

Set conditional Authentication.

Save
Go to BTP
Security à Trust à Add - Identity Authentication Tenant / Trusted Identity Provider
& Add-Trusted identity Provider & upload the IAS metadata which you have downloaded




Click on the Add-Trusted identity Provider & upload the IAS metadata which you have downloaded.


Identity Authentication Service Account Configuration
Create a group in IAS tenant for “Administrators” of Cloud Platform mobile services
Login to IAS


Go to Applications and Budled Applications (Assertion Attribuites)

Cloud Platform Account Configuration
Now, the Cloud Platform account needs to be configured to map the IAS_CPms_Admin group to a group that is granted the desired roles.
Navigate to the “Authorization Management” screen in Cloud Platform cockpit. Go to the “Groups” tab and click on “New Group”. Create a new group called “MobileServiceAdmin

Similarly create Group “MobileServiceUser” and assign the roles mentioned. This is required for Mobile app users.
SCP/BTP - Navigate to Trust Management screen, click on “Application Identity Provider” tab and click on the trusted IdP setting that represents the IAS tenant account
Login to BTP
Similarly add the Group for Mobile App user



Now, navigate to “Configure development & Operations Cockpit” (refer to the screen in step 5) and click on “Roles”. Create a new role “MobileServicesCockpitAdministrator” and assign it to the group “MobileServiceAdmin”.


Click on “Destinations & Permissions”. Edit the application permissions and select the role “MobileServicesCockpitAdministrator” and save.

Flow chart for Troubleshooting the issue.

- SAP Managed Tags:
- SAP Mobile Services
Labels:
4 Comments
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Labels in this area
-
ABAP CDS Views - CDC (Change Data Capture)
2 -
AI
1 -
Analyze Workload Data
1 -
BTP
1 -
Business and IT Integration
2 -
Business application stu
1 -
Business Technology Platform
1 -
Business Trends
1,658 -
Business Trends
116 -
CAP
1 -
cf
1 -
Cloud Foundry
1 -
Confluent
1 -
Customer COE Basics and Fundamentals
1 -
Customer COE Latest and Greatest
3 -
Customer Data Browser app
1 -
Data Analysis Tool
1 -
data migration
1 -
data transfer
1 -
Datasphere
2 -
Event Information
1,400 -
Event Information
75 -
Expert
1 -
Expert Insights
177 -
Expert Insights
357 -
General
1 -
Google cloud
1 -
Google Next'24
1 -
GraphQL
1 -
Kafka
1 -
Life at SAP
780 -
Life at SAP
14 -
Migrate your Data App
1 -
MTA
1 -
Network Performance Analysis
1 -
NodeJS
1 -
PDF
1 -
POC
1 -
Product Updates
4,575 -
Product Updates
398 -
Replication Flow
1 -
REST API
1 -
RisewithSAP
1 -
SAP BTP
1 -
SAP BTP Cloud Foundry
1 -
SAP Cloud ALM
1 -
SAP Cloud Application Programming Model
1 -
SAP Datasphere
2 -
SAP S4HANA Cloud
1 -
SAP S4HANA Migration Cockpit
1 -
Technology Updates
6,871 -
Technology Updates
493 -
Workload Fluctuations
1
Related Content
- Use Cases of Generative AI in SAP Cloud ALM in Technology Blogs by Members
- How to configure periodic import jobs in Change Request Management in Technology Q&A
- Enabling In-Order processing with SAP Integration Suite, advanced event mesh Partitioned Queues in Technology Blogs by SAP
- SAP BTP FAQs - Part 3 (Security) in Technology Blogs by SAP
- Calling Fragment Form & Send it as an attachment using ABAP Walk-Through in Technology Blogs by Members
Top kudoed authors
| User | Count |
|---|---|
| 20 | |
| 11 | |
| 8 | |
| 8 | |
| 7 | |
| 7 | |
| 7 | |
| 6 | |
| 6 | |
| 6 |