- SAP Community
- Products and Technology
- Technology
- Technology Q&A
- Cloud Identity Services - Restrict Logon to Corpor...
- Subscribe to RSS Feed
- Mark Question as New
- Mark Question as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Cloud Identity Services - Restrict Logon to Corporate Identity Provider groups without IAS sync
- Subscribe to RSS Feed
- Mark Question as New
- Mark Question as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 11-21-2023 3:36 PM
Hi,
I configured Entra ID (Azure AD) as Corporate Identity Provider. Then I setup one of my apps to use Azure AD as the default IdP. Everything works fine, and I can also map role collections in the BTP subaccount from groups in Azure AD.
The problem is that absolutely all AAD users can login now if they know the link, no matter to what groups or apps they belong. They don't get any role assigned if they don't belong to a group, so they can't do anything after logging in, but they get created as shadow users in the subaccount.
I would like to prevent the logon based on groups and I found the documentation on how to do that by configuring the "Corporate IdP Identity Federation".
However, this setup assumes that users exist in the IAS tenant and they belong to IAS groups. What I want is to just use IAS as a proxy and to not even create the users in the IAS tenant as I have now.
Is it possible to do that? Or is it mandatory to sync the corporate IdP users in IAS?
- SAP Managed Tags:
- SAP Cloud Identity Services
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Report Inappropriate Content
Hi Marcal,
You can choose not use IAS as user store and just have your user in your Azure IdP and target systems with the right permissions.
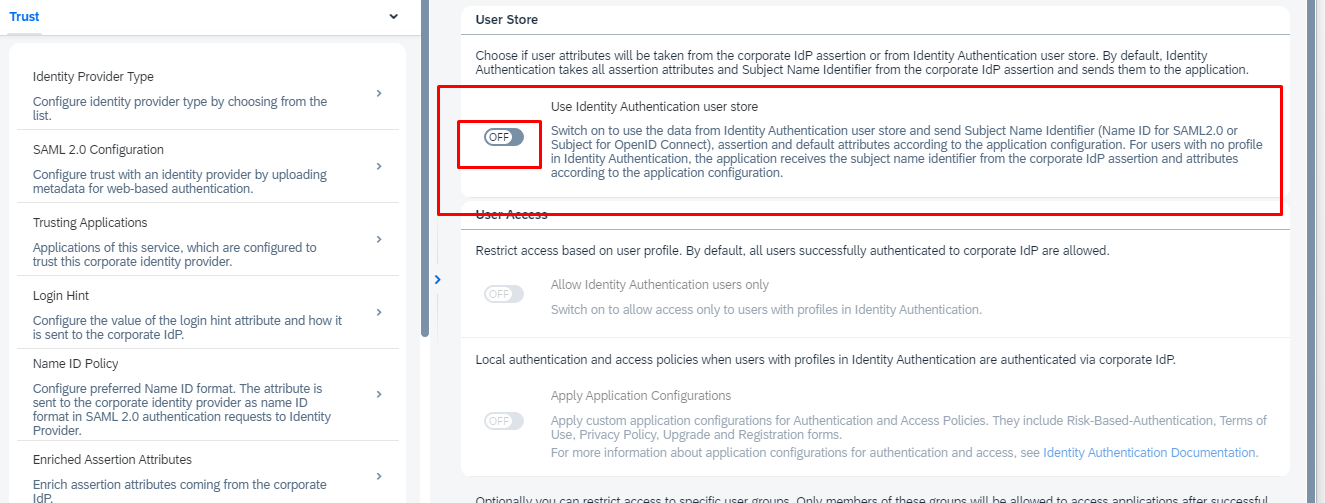
In IAS go to your Corporate Identity Provider >Identity Federation
Then turn off User store for IAS by choosing option one:
For more detail please check the link:
Thanks,
Amin
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Report Inappropriate Content
- Blank page when accessing Fiori applications on BTP in Technology Q&A
- Consuming SAP with SAP Build Apps - Web App in SAP Build Work Zone, standard edition in Technology Blogs by SAP
- providing IAS authentication through cloud identity service for UI5 MTA app in Technology Q&A
- OIDC configuration in S/4 in Technology Q&A
- SAP Cloud ALM and Identity Authentication Service (IAS) in Technology Blogs by SAP
| User | Count |
|---|---|
| 77 | |
| 9 | |
| 9 | |
| 7 | |
| 7 | |
| 6 | |
| 5 | |
| 5 | |
| 5 | |
| 5 |
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.