SAP requires that its products and supporting services meet the security requirements set by the company. Inevitably, though, with SAP’s variety, complexity, and rate of change in the organization a...

RISE provides the opportunity for SAP Basis administrators to focus on higher value activities. Cybersecurity (or information security, depending on one’s career trajectory) grew out of infrastructure...

In this age of swift technological progression and changing regulatory landscape, businesses are progressively capitalizing on data, artificial intelligence (AI), machine learning (ML), and cloud tec...
Discover how SAP secures over 6,000 AWS accounts with automated scanning and alerting.Learn how our "Secure by Default" approach, leveraging cloud security tools, enhances security posture, scalabilit...

Cyber security research reports are great sources to understand adversary techniques and threats we need to defend against. The three reports discussed in this article do exactly that. Many of those t...

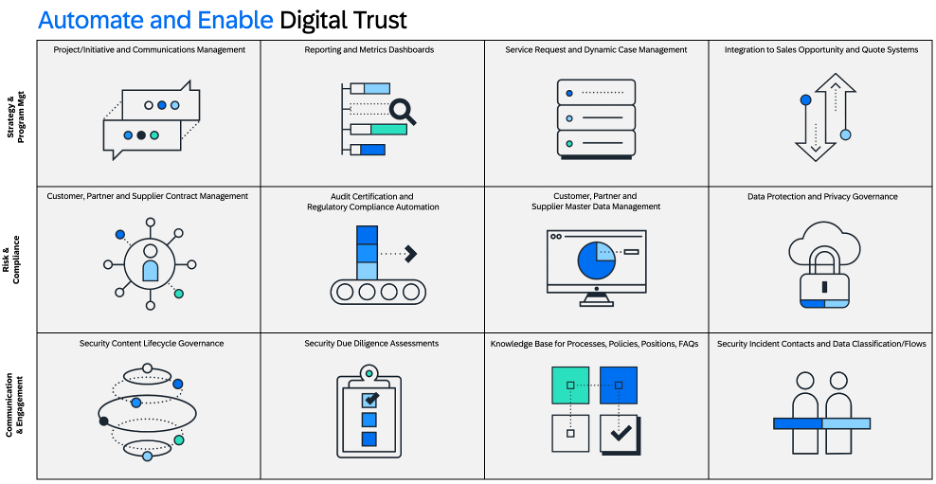
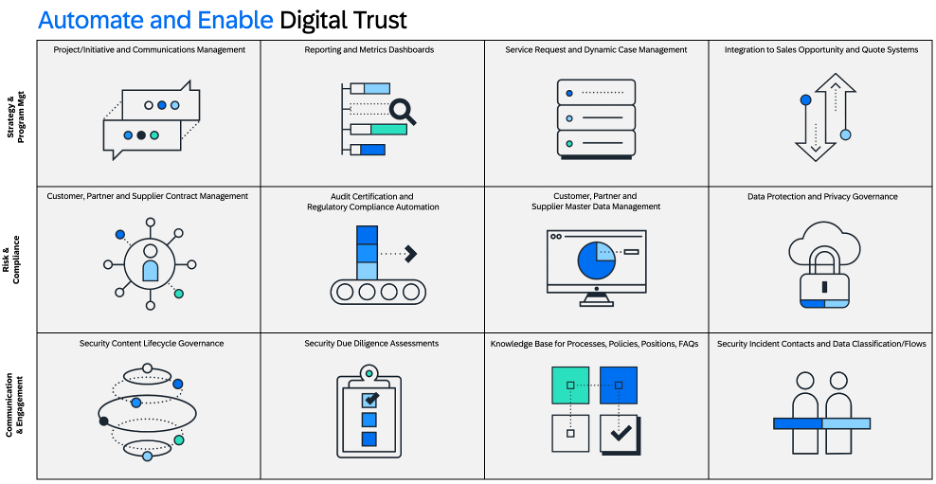
With cybersecurity threats and regulations rising, business leaders are increasingly aware of the criticality of security and compliance to business operations. Nevertheless, both cybersecurity- and E...